OWASP Just Drew a New Map, Read It Before Your Auditors Do
The Foundation's new strategic plan is not a community update. It commits OWASP to setting the technical floor for AI …

Andrew Stevens is an executive leader, investor, and technology strategist focused on the intersection of cloud, data, AI, and security. He has helped scale technology ventures from early traction to acquisition, working across fintech, media, gaming, and AI-driven businesses in both European and U.S. markets.
Known for bringing clarity to complex technology shifts, Andrew helps founders, operators, and executive teams turn emerging capabilities into practical advantage. His work focuses on AI strategy, resilient infrastructure, governance, and the operating models required to scale modern technology businesses with confidence.
The Foundation's new strategic plan is not a community update. It commits OWASP to setting the technical floor for AI …

The series finale. Across four posts, we identified three machine-speed problems - discovery, intelligence, identity - …

Non-human identities now outnumber humans by 40:1, 100:1, and in hyper-automated environments by 500:1. When AI agents …

Anthropic's $100M Project Glasswing is the first attempt to flip the economics of AI-driven vulnerability research …

AI-driven discovery has lowered the cost of finding bugs by an order of magnitude. The cost of proving which ones are …
Claude Mythos surfaced 271 vulnerabilities in a single Firefox evaluation pass. The number isn't the story - the …

The four pillars of the autonomous enterprise describe the operating model. GATE names the framework that makes it …

Prompt guardrails are not governance. When AI agents can take real-world actions at machine speed, you need …

Intelligence, data, and control only create advantage when the process layer can keep up. Adaptive workflows are where …

As enterprises move to machine-speed execution, governance has to move with them. That means embedding control into the …

Autonomy depends on data the enterprise can act on. The clean data core is what turns trusted context into operational …

Agentic AI marks the shift from assistive tools to execution systems, but only when supported by trusted data, …

Digital transformation made the enterprise modern. The next step is building one that can sense, decide, and act with …

Bringing together all 16 primitives into a single, coherent architecture. The capstone: Operational Risk Modeling.

The ultimate safety primitive: defining when humans intervene, approve, constrain, or override autonomous decisions.

Traditional telemetry cannot explain LLM reasoning. Agent systems need semantic-level visibility: reasoning graphs, …
Agents increasingly rely on long-term memory, embeddings, caches, and shared state. We need strong security and …
Agents need a control plane. Routing, scheduling, failover, cost-aware prioritization, and cross-agent coordination must …

Infinite task loops and runaway agents are already common failure modes. We need quota systems, throttling, and …
Like microservices, agents need versioning, deployment pipelines, and safe deprecation paths.

Agents need a standardized, authenticated, encrypted, and versioned protocol for inter-agent communication. Right now it …

Agents that act autonomously must obey provable invariants. Formal verification provides the missing guardrails for …

Debugging agents is nearly impossible today. We need the ability to record and replay runs deterministically to diagnose …

Models need to withstand data poisoning, prompt injection, and inversion attacks. A cleverly crafted input can collapse …
Why autonomous agents need hard limits, circuit breakers, and emergency stop mechanisms to prevent runaway execution and …

How to make every agent action tamper proof and cryptographically verifiable for compliance and forensic analysis.

Guardrails must be enforced at runtime, not left as developer best practices. Just like infrastructure-as-code, …

Go beyond API keys. Learn to engineer trustworthy AI agents with verifiable identity and attestation using the SPIFFE …

Why prompt injection is a critical vulnerability for AI agents. This guide covers detection techniques, architectural …

The next instalment in our series on trustworthy AI agents—an overview of 12 missing engineering primitives (encryption, …

An overview of missing engineering primitives (encryption, identity, governance, orchestration, observability) required …

AI agents are a powerful new tool, but they also represent a growing security blind spot. Traditional security models …

A technical guide to creating a cost-effective, serverless pipeline for streaming CrowdStrike Falcon events directly …

In our latest podcast, we speak with Andreea, Head of Data at Xapo Bank, about how AI is reshaping finance. Discover how …

The Model Context Protocol (MCP) is an emerging AI standard that enables secure, real-time context and tool integration …

Learn how to secure AI agents and protect sensitive data with Role-Based Access Control (RBAC) on Google Cloud's Vertex …

How is AI transforming baseball? In this episode of Hot or Hype, we explore how the San Francisco Giants are using AI …
Dive into our second Hot Or Hype podcast episode as we explore the buzz around AI Agents. Are they just super-powered …
Join our deep dive into AI-driven predictive analytics—explore real-world applications, potential pitfalls, and expert …

Is AI-driven predictive analytics the future of business intelligence or just another overhyped trend? In this episode …

How I optimize GCP costs with a FinOps-driven framework. Track actionable strategies, tools, and templates to reduce …
Discover how combining Ray and Vertex AI creates a complete solution for scalable AI. Our team takes a look at training, …

Thoughts on best practices for scaling AI models with cloud computing, including MLOps, cost optimization, and …

My key insights from the 2024 DORA Report, focusing on the evolution of AI integration, platform engineering, and …

Our CTO writes about how cloud platforms like AWS, GCP, and Azure accelerate AI adoption with scalable infrastructure, …
What are the core principles and best practices for building a modern data architecture? Our opinion on scalable design …

How to build an AI-first cloud strategy, integrating scalable architectures, data governance, and machine learning for …

How is the EU AI Act is shaping global AI development? Here are some compliance strategies and industry-specific …

What are the implications of the EU AI Act for global businesses in banking, ecommerce, and gaming. How can data …

How Sakura's advanced analytics and machine learning optimizes advertising campaigns. We deliver robust data pipelines, …

This guide explores key considerations for marketers to ensure compliance while maintaining ethical, effective …
The Sakura team looks at ethical AI issues for data scientists and engineers, focusing on transparency, accountability, …
Multiple Imputation strategies and key considerations tailored for data engineers and data scientists in the financial …

Understand Data Mesh principles, tools, and best practices for implementing a decentralized data architecture. Learn …
A modern, scalable, and efficient data analytics pipeline that transforms raw data into actionable insights, utilizing …

Strategies for detecting and mitigating bias to ensure fairness and equity in artificial intelligence.

TileDB, PrestoDB, TensorFlow, Dask, Zarr, and Apache Arrow can transform data management and analytics in the financial …
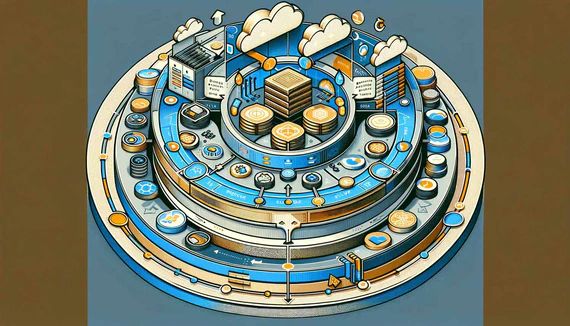
Azure services like Data Factory, Databricks, and SQL Server offer significant benefits when aligned with the Medallion …

Terraform, a powerful Infrastructure as Code tool, can be leveraged to implement effective data governance in your cloud …

Privacy by Design and its importance in data engineering.

An overview of the principles of zero trust security can be applied to a medallion architecture within a data lakehouse
Delve into the ten most critical concerns for API security.

Starting with the right pattern is important and you may be considering approaches such as a data warehouse, a data …

15 concerns in cloud security

Implementing Zero Trust for containers can help organizations secure their dynamic containerized environments and …
Implementing Zero Trust for containers can help organizations secure their dynamic containerized environments and …
DevSecOps, an approach that integrates security practices into the continuous delivery pipeline, promises to improve the …
Medallion architecture is a design pattern for data lakehouses that helps organizations effectively manage and analyze …
The data lakehouse concept has emerged as a new approach to address the limitations of traditional data lakes and data …

In the age of data-driven decision making, effective data governance has become increasingly important for businesses of …

Data literacy is the ability to read, analyze, interpret, and communicate data effectively.

Data literacy is the ability to read, analyze, interpret, and communicate data effectively.
Data architecture is the backbone of an organization's data management strategy, providing the structure and guidelines …
As data-driven solutions and artificial intelligence (AI) become increasingly prevalent, organizations must prioritize …

Effective data access and sharing practices are crucial for organizations to facilitate collaboration, drive innovation, …

Data Lifecycle Management (DLM) is a critical aspect of data governance, involving the systematic management of data …

Data integration is a critical process for organizations looking to combine data from multiple sources, systems, and …

Data stewardship plays a crucial role in any successful data governance program

Safeguarding Your Organization's Most Valuable Asset.

Data quality is a critical component of any data governance program.

Why an Infrastructure as Code approach with HashiCorp Terraform is best practice.

Questions to ask yourself to determine how assets are at risk from a cyberattack.
Accelerate your operations with proven expertise built to scale and adapt.
Enable, automate, and govern the intelligent systems that keep your business moving.